When the voice on the line sounds like your CEO: Navigating the new era of Al-driven social engineering
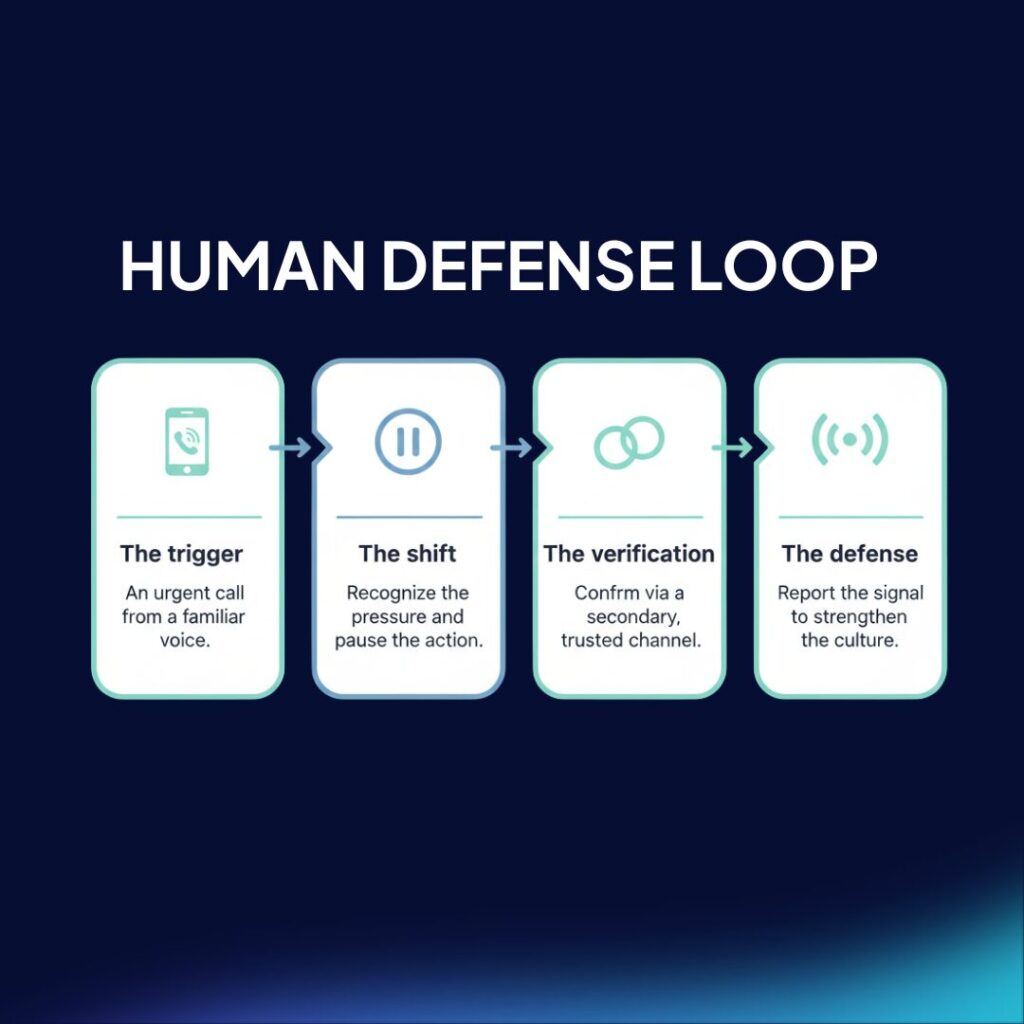
A recent incident involving a retail business highlights a critical shift in social engineering: attackers are now using AI-cloned voices to divert payments, moving past traditional email phishing. While technical filters remain necessary, they cannot see or block a conversation between two humans where trust is the primary exploit. This post argues that organizations must move beyond the “weakest link” mentality to build durable behavioral proficiency and verification protocols that survive high-pressure, high-fidelity attacks.
The leak of 47 political leaders: A case study in context-driven risk

A recent breach has exposed the personal data of 47 high-profile Spanish politicians, including regional presidents and high-ranking officials. The leak includes highly granular details: from national ID numbers to gas meter codes. For security leaders, this incident serves as a critical case study: exposed PII (Personally Identifiable Information) is not just a privacy failure; it is the ammunition for the next wave of hyper-personalized social engineering. We explore why context is the new weapon and how organizations must build a capable human defense layer to withstand it.
Zepo Intelligence Raises $15M Seed Round to Protect Workspaces from AI-Driven Social Engineering

Zepo Intelligence, the company redefining human-centric security, announced today the closing of a $15 million Seed investment round. The round includes three European VCs with strong focus in cybersecurity, Kibo Ventures, eCAPITAL and TIN Capital, and will allow Zepo to expand its team and scale its proprietary technology globally as AI-driven social engineering rapidly escalates into one of the most persistent and costly challenges for security leaders in modern organizations.
Black Friday scams: a practical guide for employees to stay safe online

Black Friday is prime time for online shopping, and for cybercriminals. Employees need practical guidance to spot fake websites, fraudulent gift cards, and scam delivery alerts. This guide equips teams with actionable tips to protect personal and corporate data, reduce malware risk, and prevent attackers from gaining a foothold in company systems.
How to run a successful phishing simulation campaign in your company? 5 essential tips

Learn how to conduct an effective employee phishing simulation campaign, raising the level of cybersecurity awareness among your employees and reducing the business costs that a cyberattack can cause.
5 emotions used in social engineering to steal your personal data

Social engineering is a psychological manipulation technique used to deceive, persuade, or influence people in order to obtain confidential information, access systems, or perform unauthorized actions. In this article, we will look at the emotions that cybercriminals seek to arouse in their victims to make them fall into their trap.
