Deepfakes don’t exploit technology gaps. They exploit obedience.
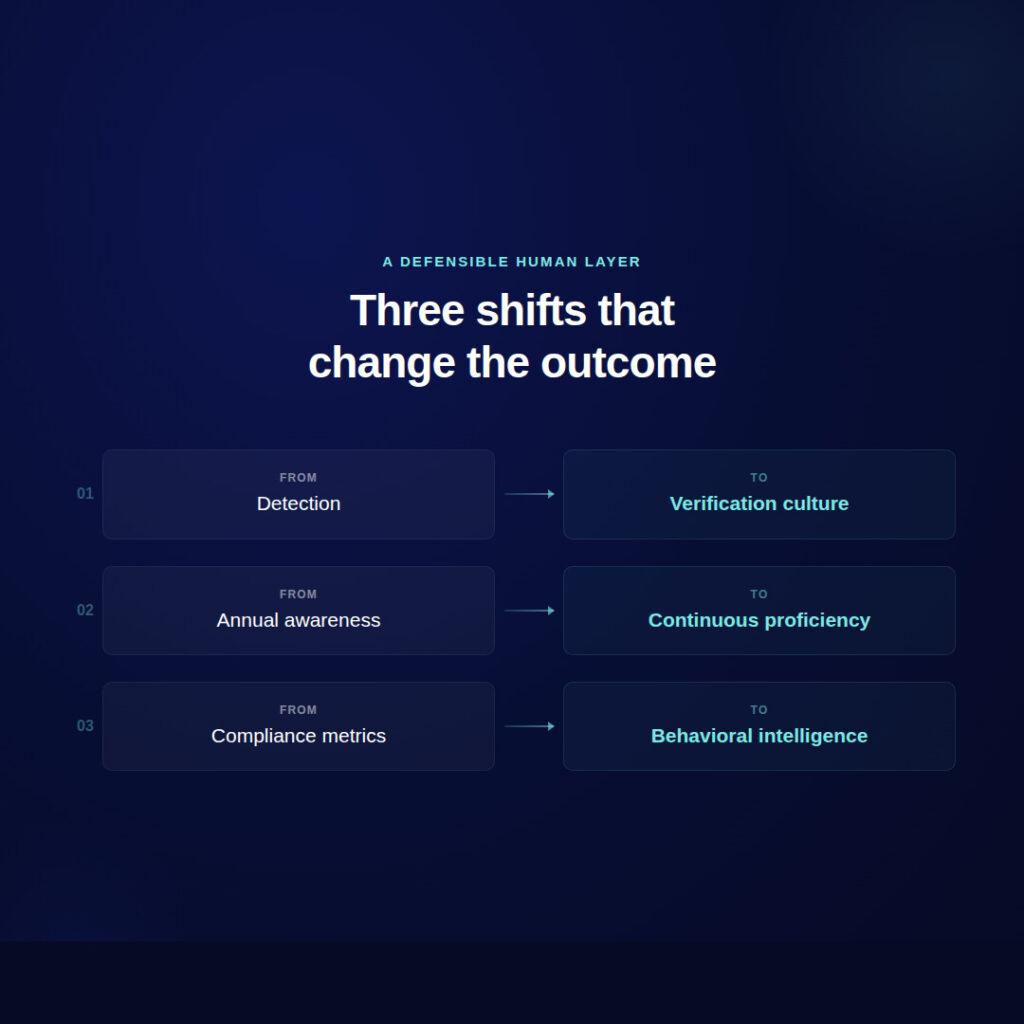
99% of security leaders say they’re confident in their deepfake defenses. The average detection score is 44%. This post argues the industry is solving the wrong problem — and that verification culture, not detection technology, is the defensible response to AI-powered social engineering.
When the voice on the line sounds like your CEO: Navigating the new era of Al-driven social engineering
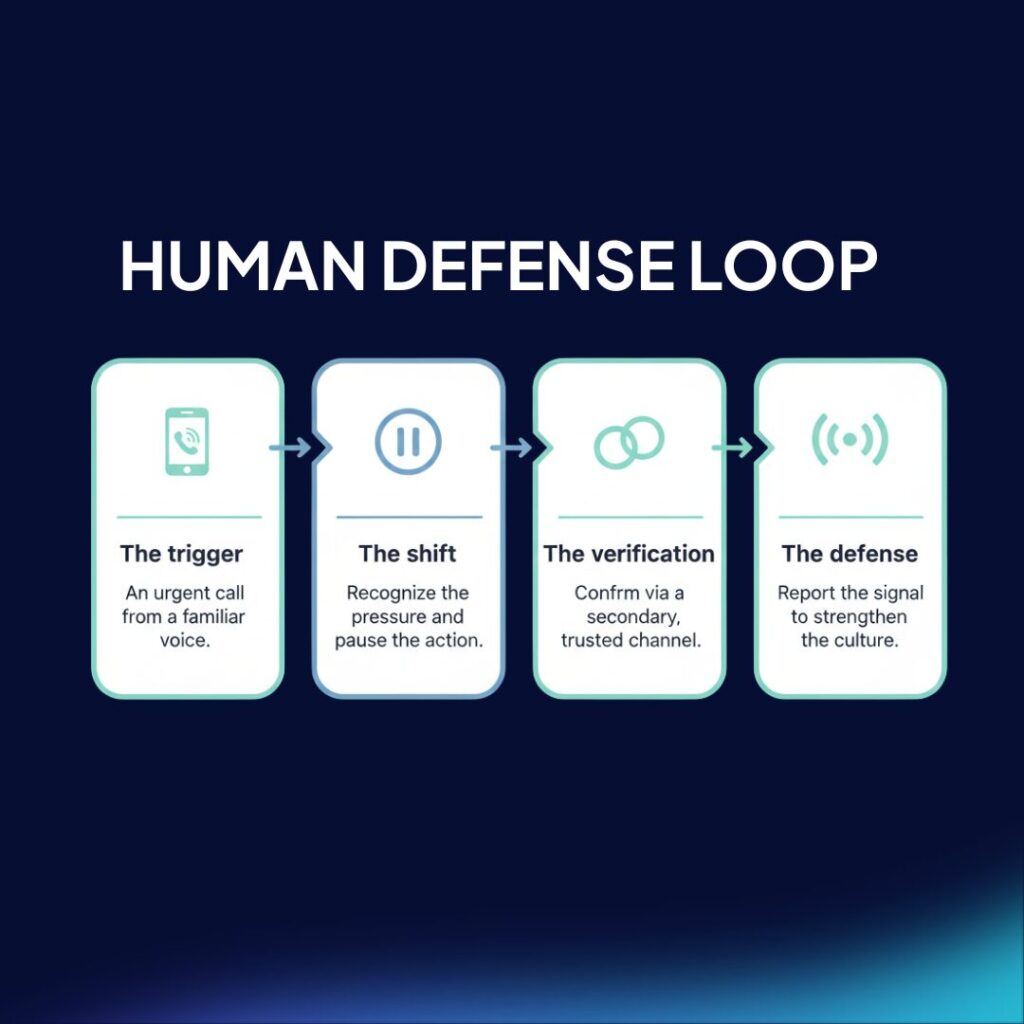
A recent incident involving a retail business highlights a critical shift in social engineering: attackers are now using AI-cloned voices to divert payments, moving past traditional email phishing. While technical filters remain necessary, they cannot see or block a conversation between two humans where trust is the primary exploit. This post argues that organizations must move beyond the “weakest link” mentality to build durable behavioral proficiency and verification protocols that survive high-pressure, high-fidelity attacks.
The leak of 47 political leaders: A case study in context-driven risk

A recent breach has exposed the personal data of 47 high-profile Spanish politicians, including regional presidents and high-ranking officials. The leak includes highly granular details: from national ID numbers to gas meter codes. For security leaders, this incident serves as a critical case study: exposed PII (Personally Identifiable Information) is not just a privacy failure; it is the ammunition for the next wave of hyper-personalized social engineering. We explore why context is the new weapon and how organizations must build a capable human defense layer to withstand it.
Zepo Intelligence Selected for the 2026 CrowdStrike, AWS & NVIDIA Cybersecurity Startup Accelerator

Zepo Intelligence, an agentic social intelligence platform for workspace security, has been selected to participate in the 2026 Cybersecurity Startup Accelerator with CrowdStrike, Amazon Web Services (AWS) and NVIDIA through its Inception program, to help fuel the next generation of AI-driven cloud security innovation.
Zepo Intelligence Raises $15M Seed Round to Protect Workspaces from AI-Driven Social Engineering

Zepo Intelligence, the company redefining human-centric security, announced today the closing of a $15 million Seed investment round. The round includes three European VCs with strong focus in cybersecurity, Kibo Ventures, eCAPITAL and TIN Capital, and will allow Zepo to expand its team and scale its proprietary technology globally as AI-driven social engineering rapidly escalates into one of the most persistent and costly challenges for security leaders in modern organizations.
Tangos, technology, and trust: a recap of our week in Buenos Aires

From exclusive roundtables at Happening Costanera to the bustling floor of IT Forum Financiero, our team spent an incredible week connecting with the heartbeat of LATAM’s financial sector.
