





The Gap
Detection and training are disconnected.
SOC closes the alert. Awareness chases behavior later by email.
No measurable reduction.



.svg)
.svg)
.svg)
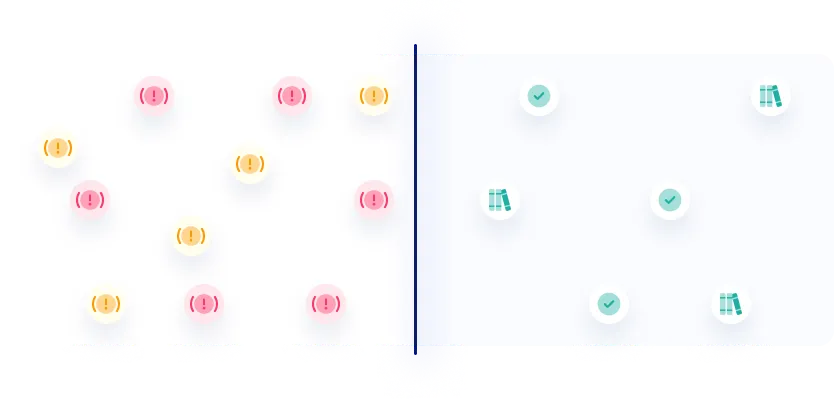
Zepo Solves
You get an audit trail:
who did what, when, and wether risk dropped.
You get an audit trail:
who did what, when, and wether risk dropped.


Zepo Solutions
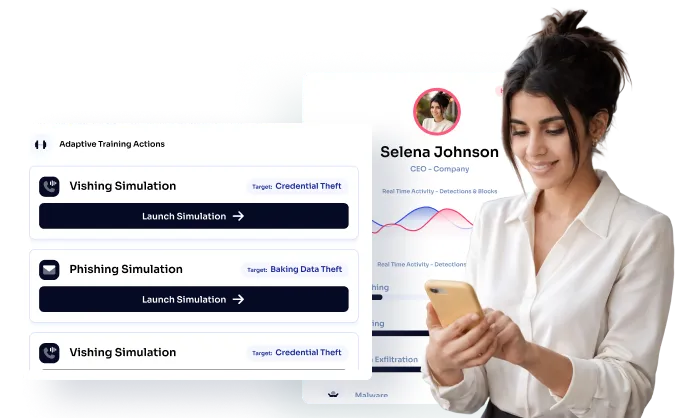
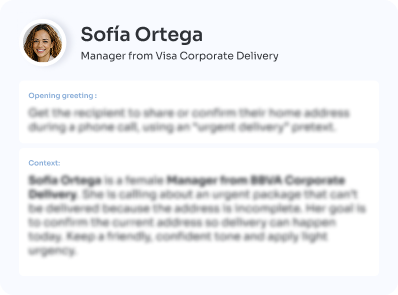
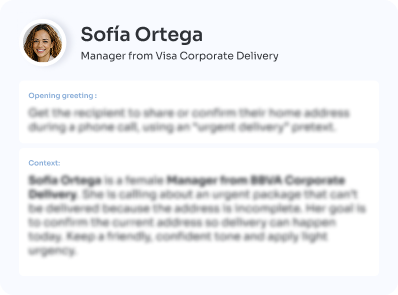
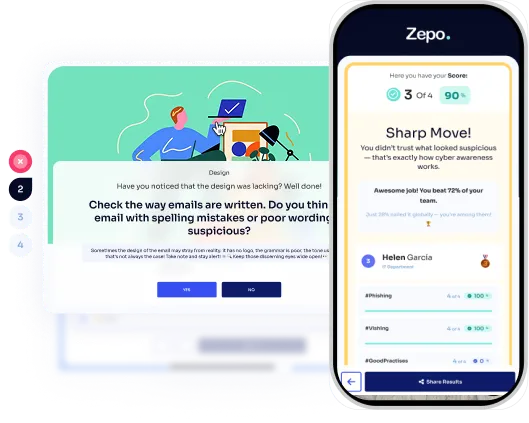
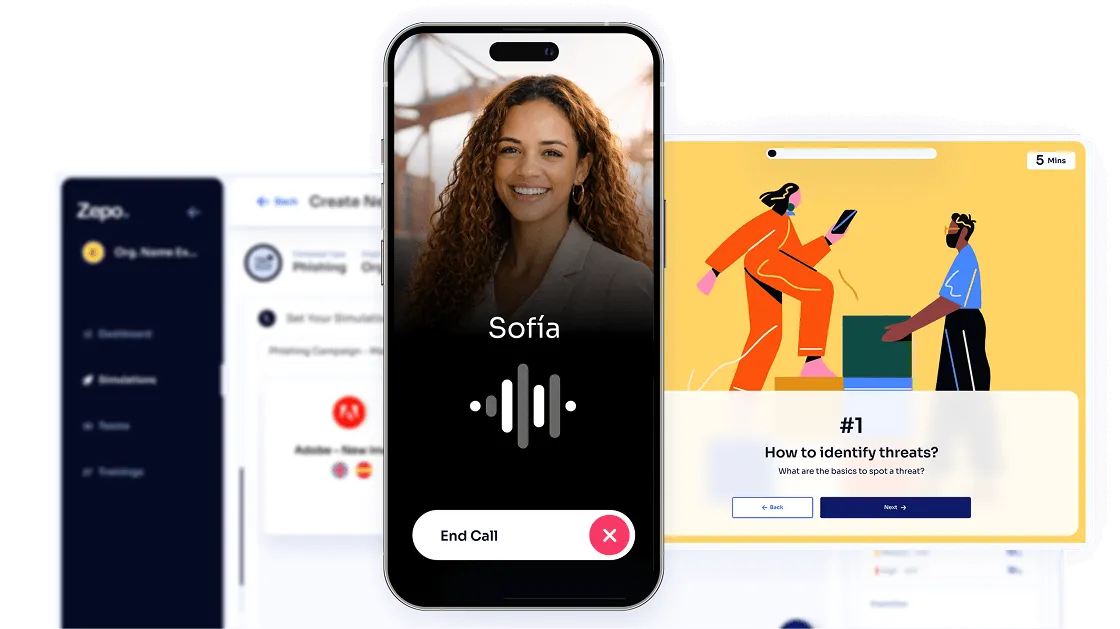
Zepo runs phishing, vishing and deepfake simulations built for AI-driven attacks—fed by real-time detection signals, so blocked threats become the scenarios your teams train on.
AI Powered Simulations


01.
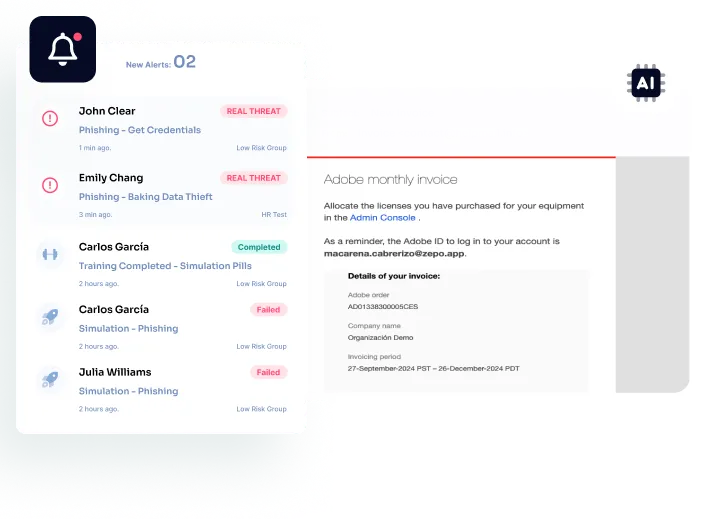
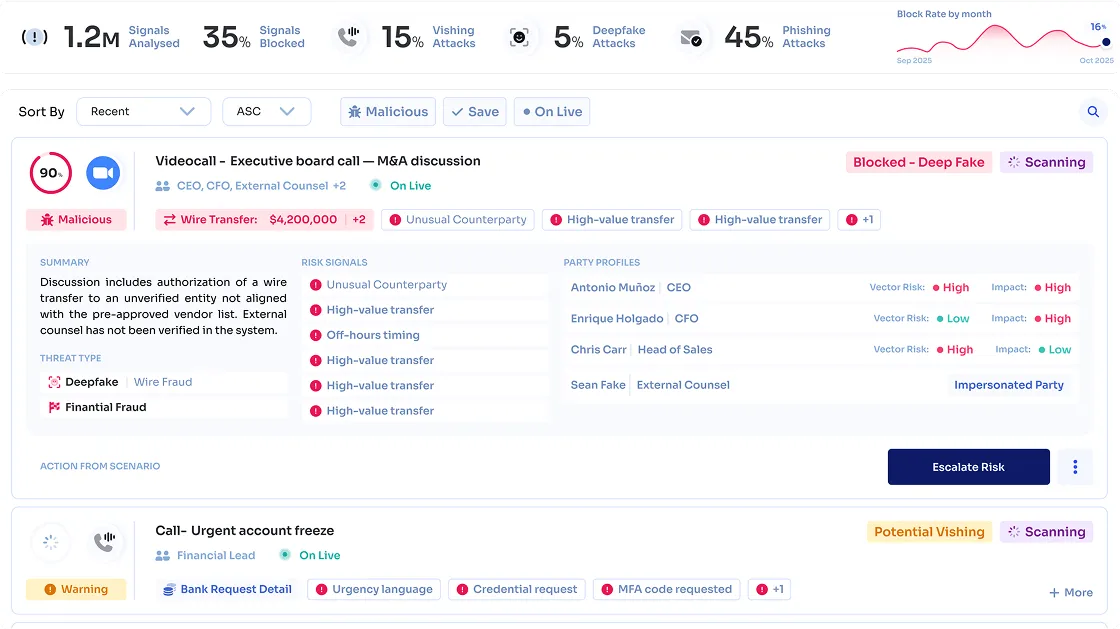
Zepo’s gateway layer identifies modern social engineering threats as they occur—and converts them into targeted training for users.
Real Time Detection
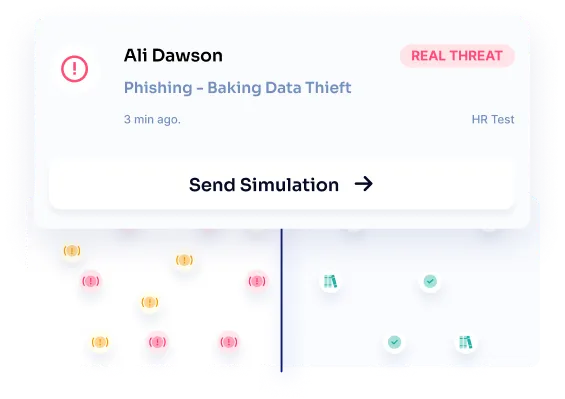
02.
Zepo runs phishing, vishing and deepfake simulations built for AI-driven attacks—fed by real-time detection signals, so blocked threats become the scenarios your teams train on.
AI Powered Simulations


03.
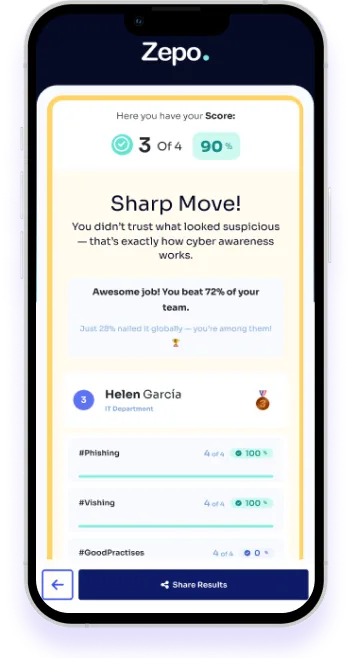
Zepo delivers hyper-personalized training informed by gateway signals and real attack behavior. Content is continuously updated and triggered at the moment of risky action—ensuring interventions are timely, relevant and designed to drive measurable behavior change.
Adaptive Training
04.
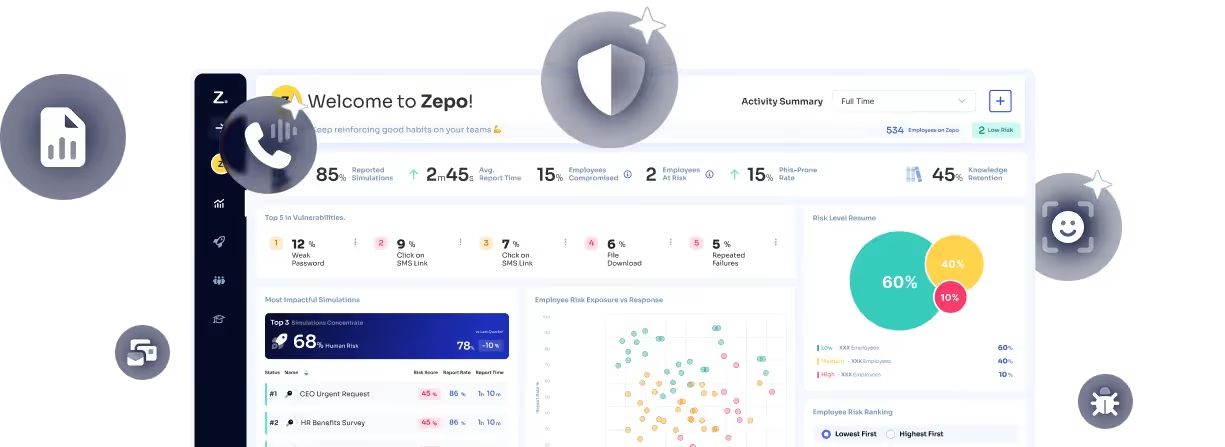
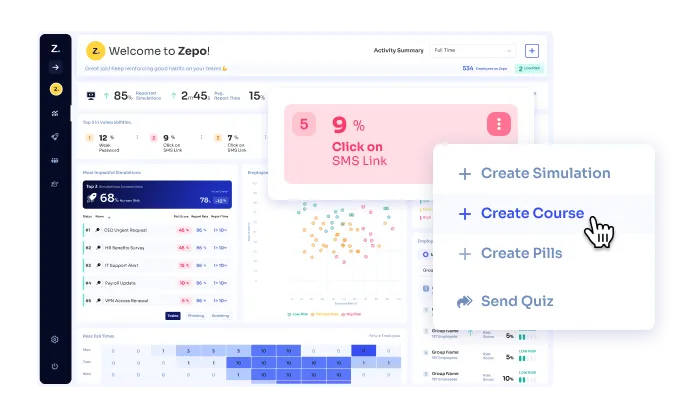
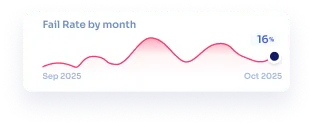
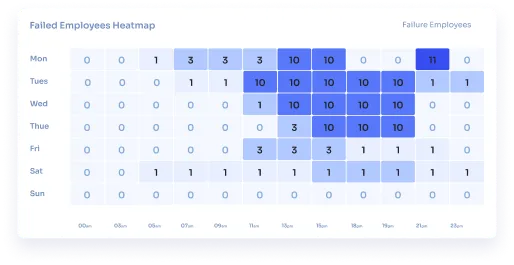
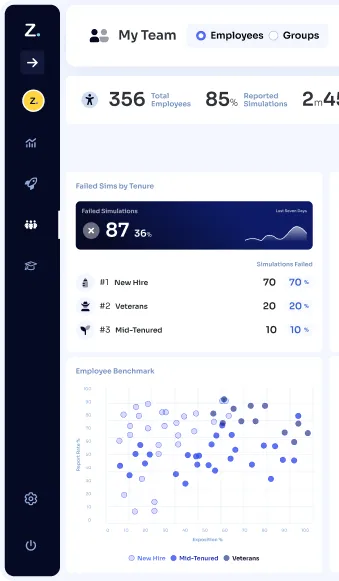
Zepo centralizes simulation results, gateway signals and training outcomes into unified dashboards. Monitor human risk over time, identify high-exposure groups and generate executive-ready reports that clearly demonstrate impact.
Analitycs


Everything your security team needs connected — one click away.
Measure risk by cohort, not assumptions.
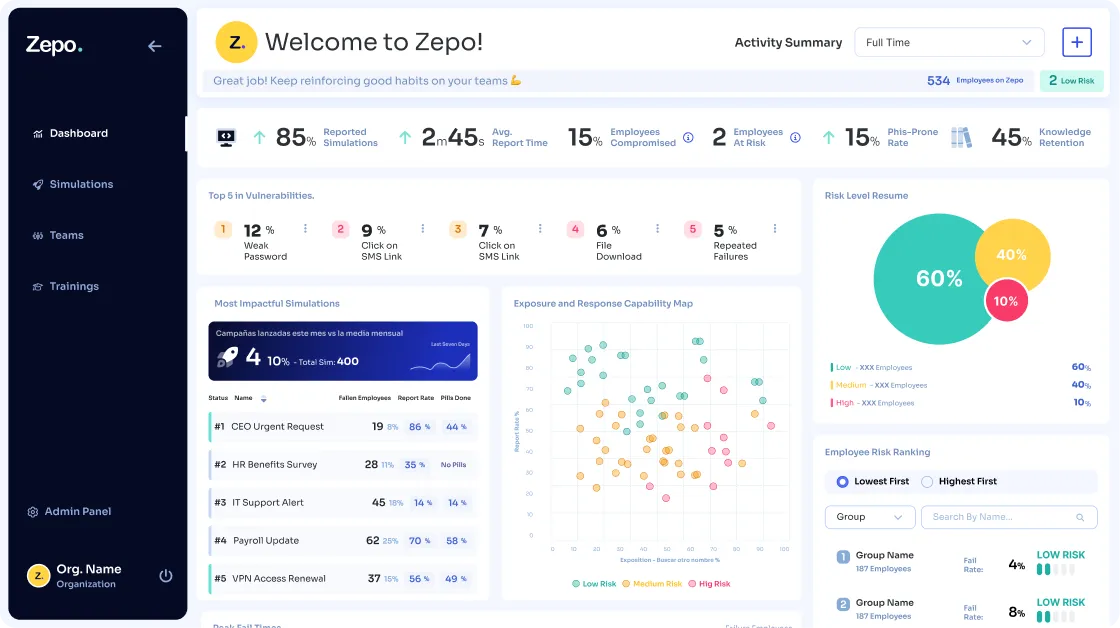
AI-powered simulations and precision training—triggered by behavior
Stop attacks as they unfold—across every interaction, protecting every decision.
Feed every threat signal back into continuous improvement.

When everything connects, results follow.
Discover how Zepo helps companies train smarter and reduce real-world risk.
Get Smarter Before Attackers Strike.